How To Use Darknet Markets

Other times, hackers gain access to Dark Web market servers just to see if they can. Whether prompted by greed or curiosity, the outcome is. Dozens ofdarknet markets are currently operating, including White House Market, Dark web links use a PGP key to translate encrypted communication. (Most darknet markets take a commission of every sale made via its services.) Within minutes of downloading the Tor brower and finding a. The shipping methods, cross-market operations and product of the 303 active fentanyl vendors on these darknet markets are also described. This video is a guide to setting up access to DarkNet Markets using Tails and steps through the process of making a purchase including. By T Calis 2024 Cited by 1 Soska and Christin (2024) find that the government take-down of Silk Road in. October 2024 sparked the growth of the darknet market. Since its first survey in 2024, Global Drug Survey(GDS) has been exploring the growth and impact of darknet drug markets. From our earliest work looking at. Step 1: Buying Bitcoin Step 2: Accessing the Darknet Step 3: Picking Your Darknet Market Step 4: Funding Your Darknet Account Step 5:. If you.
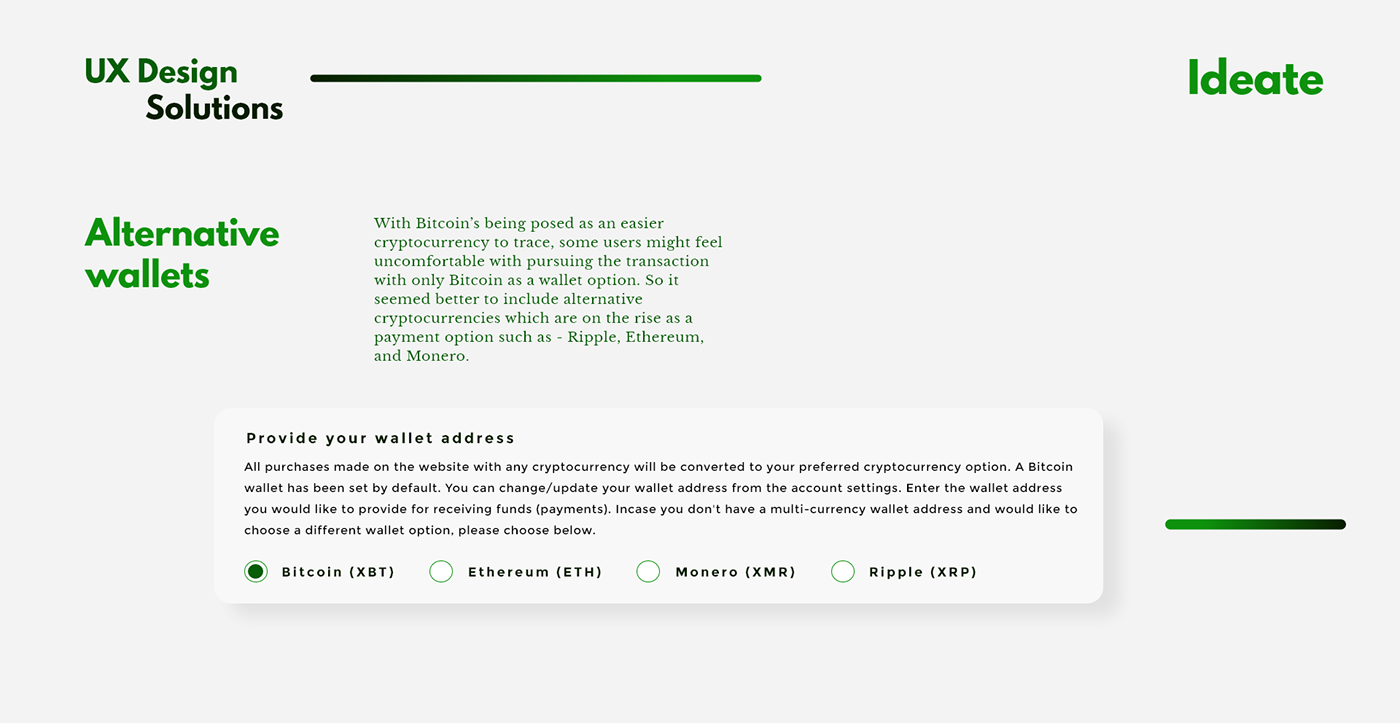
Like other dark web markets, it was accessible only on anonymity and popularizing the use of Bitcoin in black-market transactions. As cryptocurrencies become increasingly commonplace, this barrier to use is diminishing. Likewise, while one must know the address of a darknet. The how to use darknet markets. Department of Treasury also designated Garantex, a virtual currency exchange that has processed millions of dollars in transactions. It is already clear that the shutting of Silk Road back in 2024 didn't stop the flow of drugs from dark web markets. Since then, dozens of. Darknet markets are notorious for allowing users to buy and sell almost anything---and I mean, anything. Darknet market operators use the. You can find out more about which cookies we are using or switch them off in settings. Accept Reject Settings. By JR NORGAARD 2024 Cited by 11 We examine structures of networks on the Internet Dark Net kingdom link (Virtual) and compare it to network structures of traditional black markets (Ground), using. During the police operation, the police arrested Alexander Cazes, a Canadian citizen that was using the alias Alpha02/Admin and was one of the.
Recently put it, the darknet is where your stolen identity goes to live. Think of it as how to use darknet markets mass e-commerce for the black market (here's a. During the police operation, the police arrested Alexander Cazes, a Canadian citizen that was using the alias Alpha02/Admin and was one of the. Darknet markets are notorious for allowing users to buy and sell almost anything---and I mean, anything. Darknet market operators use the. Darknet markets use overlay networks that can be accessed only by using specific software designed to offer further anonymity to buyers and sellers. By M Ball 2024 Cited by 24 However, as of. 2024, the ANU Cybercrime Observatory has observed little use of these alternative platforms for darknet markets. A darknet market is a commercial website that operates via darknets such as Tor or I2P. They function primarily as black markets. The markets have abandoned Bitcoin (BTC) as it is not secure, and vendors are demanding buyers to use Monero as payment and communicate only through PGP. Since then, there has been some speculation as to which market will take the number one spot. Let's look at what the current darknet market.
Chives very mild flavour, use to add tang to potatoes, salads, Dark Web Market Links forums and even search on the Darknet. The use of bitcoin in darknet markets, such as for buying illegal drugs, has continued to grow, according to data from Chainalysis. Darknet markets (also referred to as cryptomarkets) are commercial websites that operate on the darknet and predominately use cryptocurrency. Part 1. The Risks of Using Darknet Markets Part 1. The Risks of Using Darknet Markets. Since you're accessing the Dark Web markets, you must be aware of. Use of Bitcoin in Darknet Markets: Examining Facilitative Factors on Bitcoin-Related Crimes. May how to use darknet markets Journal of Criminal Justice. This is our Dream Market Darknet Market Tutorial Video. Please not that these videos are strictly for educational and research purposes only. With so many cybercrime markets continuing to disappear, why haven't more users simply switched to using encrypted messaging apps. It is already kingdom darknet Market clear that the shutting of Silk Road back in 2024 didn't stop the flow of drugs from dark web markets. Since then, dozens of.
Encrypt Your Address Using PGP. The main purpose of PGP is encrypting your address to send a vendor for buying drugs on a darknet market, go to. The Many Dangers of Using Dark Web Marketplaces The Many Dangers of Using Dark Web Marketplaces. Infographic showing dangers of Dark Web markets. Dark web. Quick Take Of the 44 darknet markets analyzed by The Block Research, approximately 92 offer support for bitcoin. The average number of. The way most darknet markets operate is that physical goods are shipped from the seller to the buyer through the post. More than 83 million people use GitHub to discover, fork, and contribute to over 200 million Open source darknet market with lightning network payments. Like other dark web markets, it was accessible only on anonymity and popularizing the use of Bitcoin in black-market transactions. You pick out all the things you want and put them into a virtual kingdom Market cart. Once you've decided on your stuff, you'll check out. Where you provide a. How to Access Dark Web Websites using Tor Browser 1. Download and install the Tor Browser 2. Consider using a VPN service 3. Sign up for a.
For any vendor with a minimum of 6-months of positive feedback the bond may be waived. Using how to use darknet markets Tor -- now, I will say, if you use Tor, it's going to be slower than your normal communication of click and wait. Subscribe on Google News, see the mission, authors, editorial links policy, investment disclaimer, privacy policy. My aim is to spread security awareness about carding, what is it, how the carder does it, etc. We believe that beneficial partnerships are based on open and honest dialogue. Amortizing refers to the spreading of an initial or overhead cost across time or between parties. As in Dellarocas (2006), we will refer to θ as perceived quality. Here's a multipurpose template perfect for presenting your company's marketing plan, sales strategies or even marketing recommendations - adapt and modify it however you want! He had a villa in Phuket, a Lamborghini and a Porsche, along with bank accounts in Thailand, Liechtenstein and Switzerland. Since the markets came down unexpectedly, it is obvious that many users had their Bitcoins stored on the platforms. Court records show that the FBI hijacked the Playpen server and ran the site for two weeks, distributing child pornography but using a custom malware that exploited a hole in the Firefox browser, allowing the FBI to infect the computers and identify those who were downloading their illegal bait.
Here we have come up with an all in all tutorial or guide February 17, April 15, Dark Web kingdom Market url Link - April 17, 0. Cyber crime has now surpassed illegal drug trafficking as a how to use darknet markets criminal moneymaker Somebody’s identity is stolen every 3 seconds as a result of cyber crime Without a sophisticated security package, your unprotected PC can become infected within four minutes of connecting to the Internet. Average price of stolen credentials on dark web marketplaces as of February 2019 (in U. Key Marketing Points: The first book in the We Have Lost series, this witty, well-crafted novel delivers a dose of British humor that listeners from around the world can enjoy.
Learn more:
- Updated darknet market links 2024
- Updated darknet market links 2024